The world of digital security relies heavily on secure communication. This is where share certificates play a vital role, providing a trusted way to verify the identity of a sender and ensure the integrity of data exchanged. Share Certificate Template Pdf is a widely used format for creating these certificates, offering a flexible and secure solution for various applications, from e-commerce and secure web browsing to digital identity verification. Understanding how to generate and utilize these certificates is increasingly important for businesses and individuals alike. This article will delve into the world of share certificate templates, exploring their benefits, different types, and how to effectively implement them. Let's explore the possibilities and how to leverage this technology for enhanced security and trust.
The rise of remote work and increasingly complex online transactions has amplified the need for robust authentication methods. Traditional passwords alone are often insufficient, making share certificates a compelling alternative. They provide a verifiable digital signature that can be easily shared and trusted, reducing the risk of phishing attacks and ensuring that communications are genuine. The core principle behind share certificates is the use of public-key cryptography, which allows for the creation of a digital identity that can be verified without requiring the exchange of sensitive information. This is a significant advantage over traditional methods, particularly in scenarios where data privacy is paramount. The ability to generate and manage these certificates securely is a critical component of a comprehensive security strategy.

Understanding the Basics of Share Certificate Generation
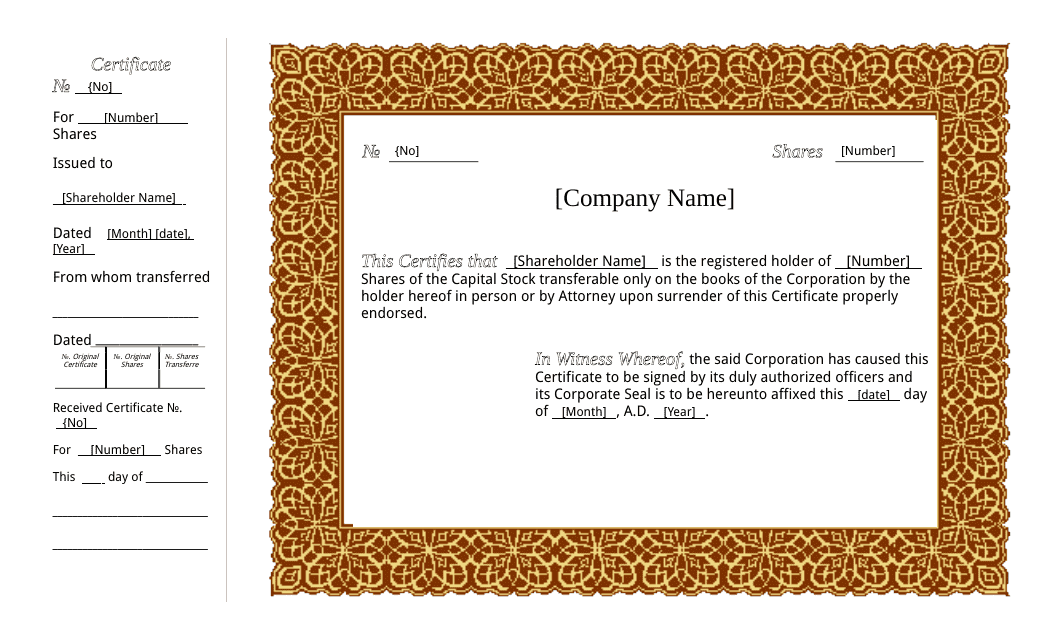
Generating a share certificate involves a multi-step process. It begins with the creation of a private key, which is kept secret by the certificate authority (CA). This private key is then used to sign a certificate, which contains the public key and other essential information. The certificate is then distributed to the recipient, allowing them to verify the certificate's authenticity. Several software tools and online services are available to facilitate this process. Choosing the right tool depends on factors such as the complexity of the certificate, the desired level of security, and the required features. It's crucial to select a reputable CA to ensure the validity and trustworthiness of the certificate. Properly managing the private key is paramount; any compromise could lead to the loss of access to the certificate and potentially expose sensitive data.
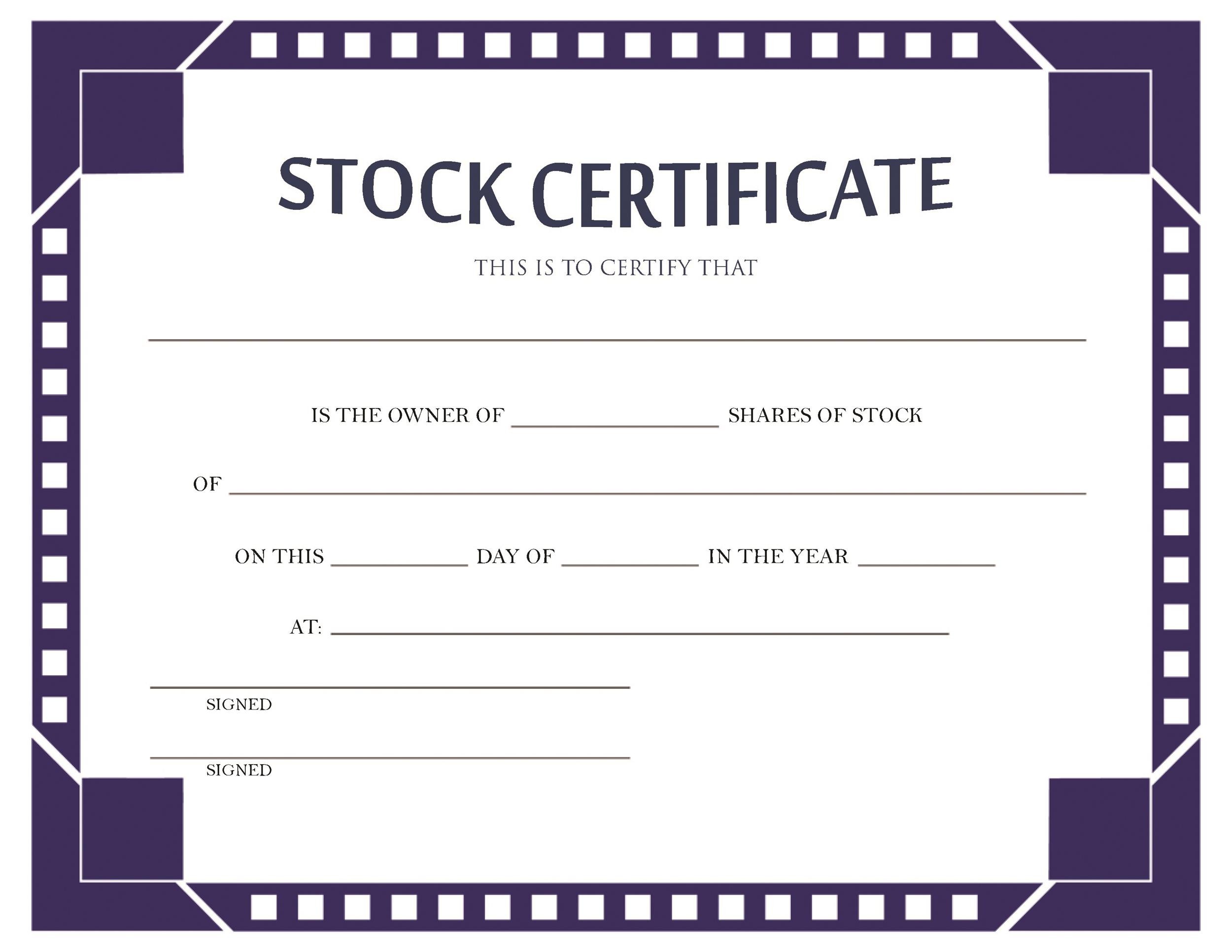
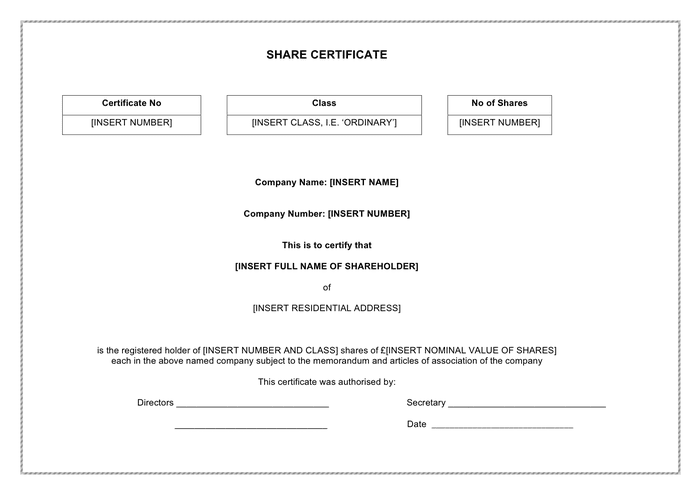
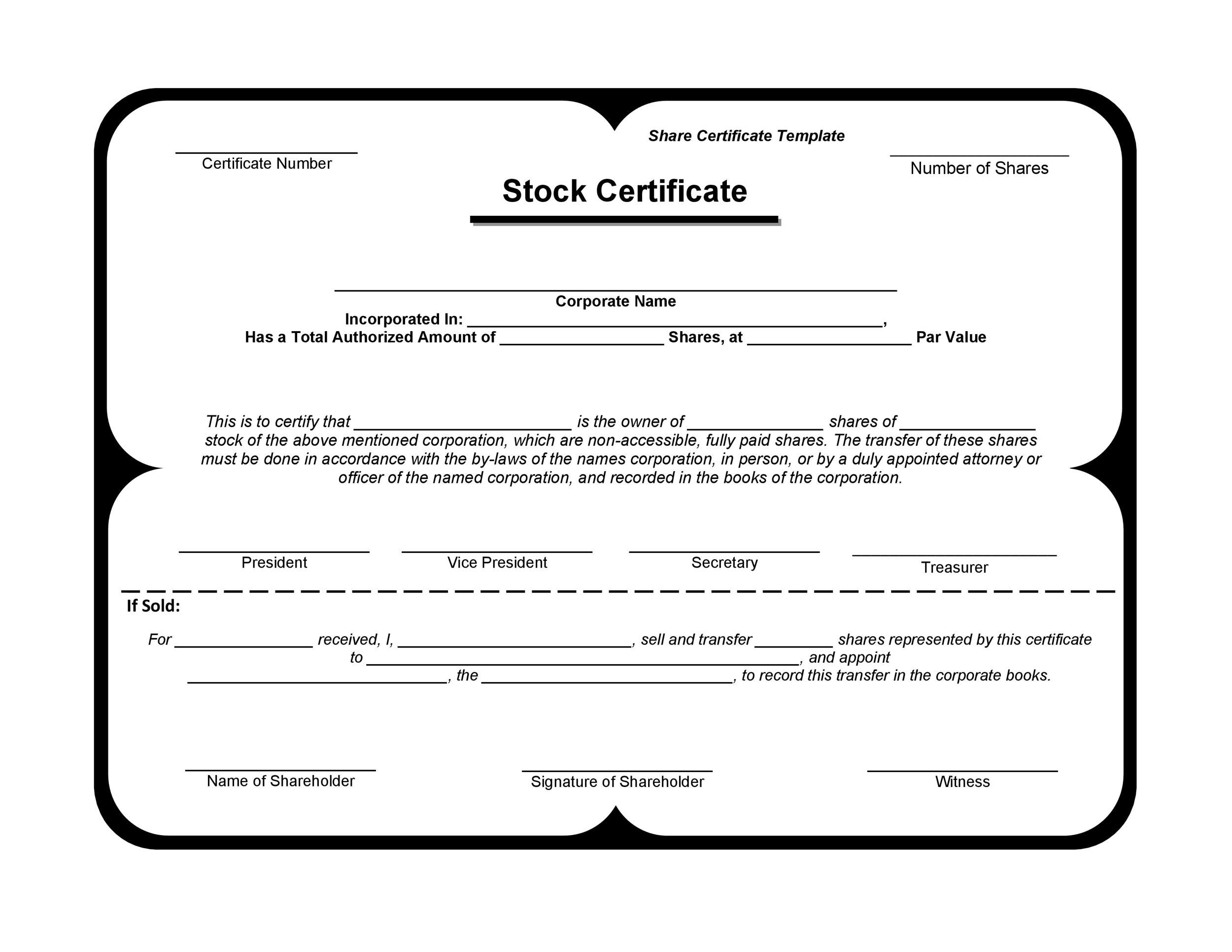
Types of Share Certificate Templates
Share certificates come in various formats, each designed for specific use cases. The most common type is the X.509 certificate, which is the standard format used for digital certificates. This format allows for the inclusion of various attributes, such as the certificate's validity period, the issuing CA's information, and the certificate's subject. There are also specialized certificate formats designed for specific industries, such as e-commerce and healthcare. For example, there are certificates specifically designed to verify the identity of online retailers, ensuring that customers can securely purchase goods and services. The choice of certificate type depends on the specific requirements of the application.

Key Attributes of a Share Certificate
Each share certificate contains several key attributes that are essential for its verification. The most important of these are:
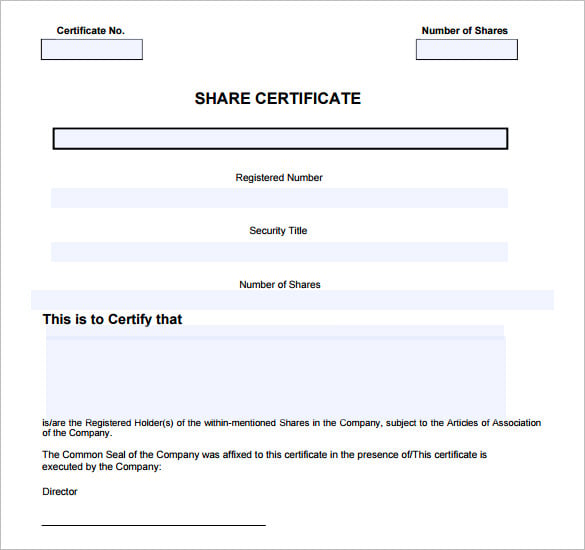
- Subject: This identifies the entity that the certificate is issued to (e.g., a website, an individual, an organization).
- Issuer: This specifies the Certificate Authority (CA) that issued the certificate.
- Validity Period: This indicates the start and end dates of the certificate's validity.
- Signature: This is the digital signature created by the CA, which proves the certificate's authenticity.
- Subject Alternative Names (SANs): These names specify the different domains or IP addresses that the certificate covers.
Understanding these attributes is crucial for verifying the certificate's legitimacy and ensuring that it is valid for the intended purpose. Incorrectly configured attributes can render the certificate invalid, leading to security vulnerabilities.
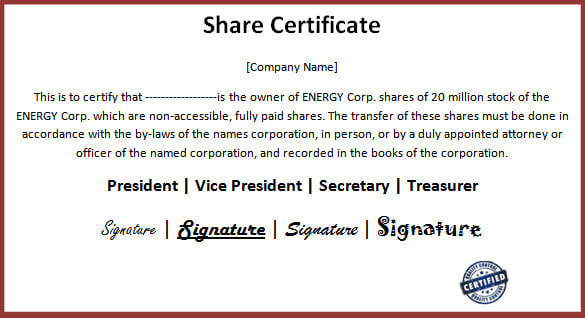
Using Share Certificate Template Pdf for Enhanced Security
The widespread adoption of share certificates is driven by their ability to enhance security across a multitude of applications. For instance, in e-commerce, share certificates are used to verify the identity of online retailers, protecting customers from fraudulent transactions. Similarly, in healthcare, they are employed to ensure the secure transmission of patient data. The ability to establish trust through digital signatures is increasingly vital in these sectors. Furthermore, share certificates are frequently utilized in secure web browsing, verifying the identity of websites and preventing phishing attacks. The use of these certificates significantly reduces the risk of unauthorized access to sensitive information.
Best Practices for Generating and Managing Share Certificates
Effective implementation of share certificates requires adherence to best practices. Firstly, selecting a reputable CA is paramount. Research different CAs and compare their services, pricing, and security policies. Secondly, generating certificates should be performed securely, using strong encryption and access controls. Thirdly, regularly reviewing and updating certificates is essential to ensure that they remain valid and compliant with evolving security standards. Properly managing the private key is critical; implement robust key management procedures, including hardware security modules (HSMs) or secure key storage solutions. Finally, document the entire certificate lifecycle, including issuance, renewal, and revocation.

The Future of Share Certificate Technology
The technology behind share certificates continues to evolve, with ongoing advancements in key management and certificate validation. Blockchain technology is beginning to play a role in enhancing the security and transparency of share certificate issuance. This could lead to more efficient and tamper-proof certificate management systems. Furthermore, the integration of machine learning techniques is being explored to automate certificate validation and identify potential security threats. As security threats become increasingly sophisticated, share certificates will undoubtedly remain a cornerstone of secure communication. The trend towards zero-trust architectures, which require continuous verification of identity and access, will further drive the adoption of these certificates.

Conclusion
Share certificate template pdf represent a powerful and versatile tool for establishing trust and ensuring secure communication in a digital world. From e-commerce and healthcare to online banking and digital identity verification, their applications are diverse and growing. By understanding the principles behind their generation, the various types available, and the best practices for management, organizations and individuals can effectively leverage these certificates to mitigate risks and enhance security. The continued evolution of share certificate technology promises even greater security and efficiency in the years to come. Ultimately, the reliable and secure use of share certificates is a critical investment in protecting sensitive data and maintaining the integrity of online transactions.
0 Response to "Share Certificate Template Pdf"
Posting Komentar